Penetration testing services for Wired Quote
Project overview
Wired Quote contacted DICEUS requesting penetration testing services to check how their web application copes with various cyber vulnerabilities and threats and discover and prevent potential issues that can cause reputation, customer trust, and revenue loss. The primary goal of this project was to provide Wired Quote with an understanding of the current level of security in the web application and its infrastructure components.
Client information
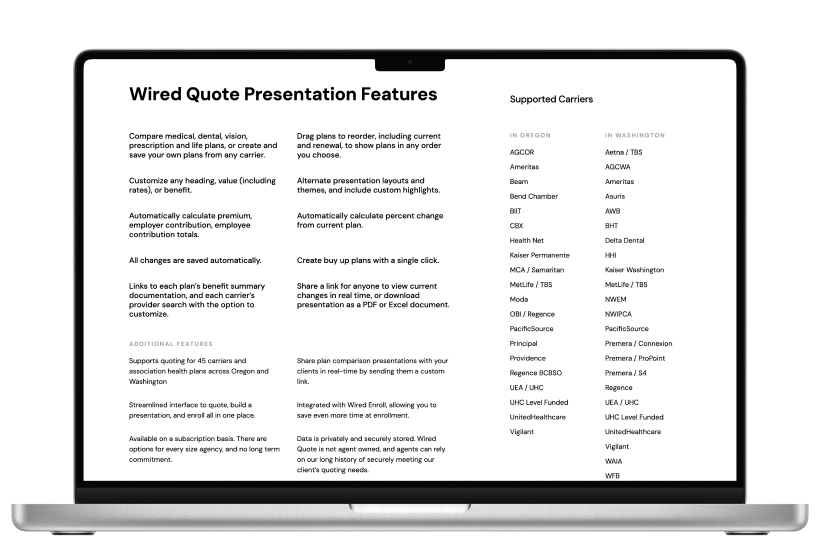
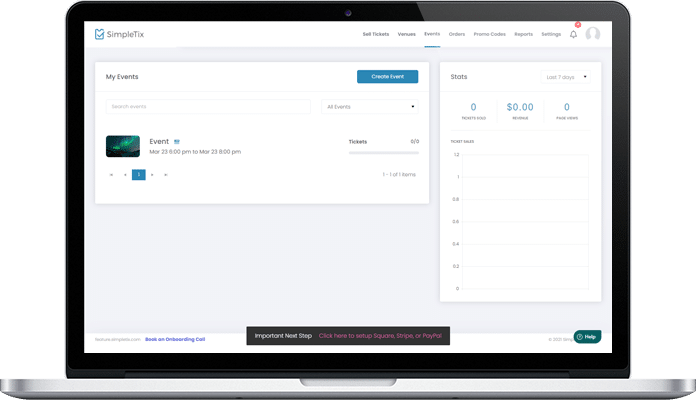
Wired Quote has served the health insurance community since 2009, offering online group quoting, presentation, and enrollment in Washington and Oregon states. The company provides an online, user‑friendly quoting tool for insurance agents that saves time, reduces costs, and helps eliminate quote errors.
Business challenge
Since Wired Quote is a fast-growing tech company that provides software for financial services, it should always take care of its reputation and security. So, they decided to check how well-prepared they were for cybersecurity issues. And pen testing is the best way to show how easy it would be for scams or cyber attackers to breach the company’s defense. Our customer contacted us to help them uncover all existing and potential vulnerabilities and develop a list of recommendations and techniques to prevent the risks.
Technical challenges
The team had to thoroughly explore the customer’s network, server devices, web apps, and all the tech stack used to build the tool.
Solution delivered
To reach the primary goal of the project, our team identified application-based threats to vulnerabilities in the application, compared Wired Quote current security measures with industry best practices, provided recommendations that Wired Quote can implement to mitigate threats and vulnerabilities and meet industry best practices.
DICEUS provided web app penetration testing services that included the following tests: application security testing, bypassing security controls like Intrusion prevention systems (IPS and WAF), testing for the latest OWASP Top 10 and SANS25 security risks (SQL-injections, XSS, SSRF, XXE, etc.), testing REST API security implementations and misconfigurations according to the OWASP API Top 10, unauthenticated and Authenticated testing, access control matrix verification, testing for vertical and horizontal privileges escalation, bypassing multi-tenancy security controls, and more.
We provided the client with a penetration testing report and remediation report including a summary of business risks, high-level recommendations, and findings details.

Let’s discuss how we can help with your project
Key features
Discovery phase
The team defined a scope for penetration testing and developed a mutual agreement to govern the parameters and limitations of testing. Also, DICEUS discovered and identified the network, security, and server devices, web applications, APIs, and network services to proceed with testing.
Grey Box testing
Vulnerability scanning and manual vulnerability assessment of identified devices and services were done. Manual and automated attempts to exploit identified vulnerabilities and web apps were also made.
Recommendations
After the testing, we developed a list of remediation techniques for the identified vulnerabilities and recommendations for technology solutions to secure the vulnerabilities discovered. The customer received a comprehensive report with the outcomes of the penetration testing project.